Every business needs to maintain cybersecurity in the workplace. This is especially true for businesses in the healthcare industry and every retail business handling customer information.

[Because cybersecurity is an ever-present requirement, this previously published post has been revised and updated.]
If your company is part of the health services industry you are already familiar with the requirements of the Health Insurance Portability and Accountability Act of 1996, commonly referred to as HIPAA. Because of the vast amount of Internet technology now being utilized in the healthcare field, the need to protect privacy and provide security of health information is more challenging than ever.
The Department of Health and Human Services (HHS) recently released new voluntary HHS cybersecurity guidelines that provide a number of strategies to cost-effectively reduce the risks associated with specific, common cybersecurity threats.
An article from Mondaq.com explains the reason for the HHS guidance,
“Cybersecurity incidents not only place sensitive information at risk, they also have the potential to affect patient care, disrupt operations, and threaten patient safety. Failing to address cybersecurity can be costly, both in terms of an organization's bottom line and the reputational damage that may follow a breach. HHS estimates that data breaches cost the United States health care system $6.2 billion in 2016 alone.”
The article goes on to note that the guidelines provided by the HHS can be applied to common cyber threats in other industries as well.
Retail Businesses are Prime Cybersecurity Targets
Cybersecurity strategy and tactics continually evolve in an attempt to stay ahead of hackers and their tactics. And because of the vast amount of customer’s personal information managed and stored by retailers, these businesses are prime targets for cyber attacks.
According a recent article on Forbes.com,
“Retail must know e-commerce is already a main target for cyber-attacks because of the rich-pickings of consumers’ personally identifiable information (PII) intrinsically linked to payment data required to complete transactions. At the very least, personal information gets stored for future use and targeted marketing.
When a retailer is hacked potentially millions of individuals fall victim to the hacker, having their information stored and sold on the dark web, ready to be merged with other data sets to build up useful profiles of the general public for identity theft and phishing campaigns.”
In response to this growing and constant threat, the EU implemented the General Data Protection Regulation (GDPR), which imposes requirements for U.S. and other organizations that process the personal data of EU residents. This means that businesses in the U.S. must ensure that they understand and document exactly what personal data they hold, as well as what data they process and transfer.
In January 2019, Google was fined €50 million , or approximately $57 million, for violating the GDPR. Google was penalized “for failing to comply with the GDPR’s transparency and notice requirements, and for failing to properly obtain consent from users for ads personalization.” To date, this represents the largest GDPR fine imposed so far.
Not to be outdone, the state of California recently passed into law the California Consumer Privacy Act of 2018 (CCPA), which becomes effective beginning January 1, 2010. The new law is intended to protect consumers with new rights over personal information collected by businesses. This includes the right to require that a business provide what information is being collected about them. to disclose what personal information it is selling, and to request that a business delete any personal information it may have collected from them.
Maintaining IT security is an ongoing task that requires continual monitoring and updated measures. Part of the task consists of regularly assessing cyber threats and data analysis to constantly monitor for signs of possible intruder access.
Cybersecurity: Preventing Identity Theft and Employee Cybercrime
The number one objective for identity theft is to steal money, directly or indirectly, with the personal information obtained. The more sophisticated cybercriminals will look to sell the stolen information, while smaller operatives tend to use it to make fraudulent purchases.
But the sobering reality is that this type of cybercrime is on the rise and increasing every year. A recent report from the Insurance Information Institute (III) reference the an identity fraud study released by Javelin Strategy & Research. The study determined that 15.4 million U.S. consumers lost a total of $16 billion in 2016 as a result of identity fraud. This is compared the $15.3 billion stolen from 13.1 million victims a year earlier.
It's been estimated that from 2010 to 2016 , identity thieves stole over $107 billion.
Because cybersecurity has become a national issue, the National Cybersecurity Protection Act of 2014 was passed and was enacted in December 2014. The act requires federal agencies to notify affected individuals of the discovery of any data breach “as expeditiously as practicable and without unreasonable delay."
In addition to this federal effort, at least forty-seven states, Washington D.C., Guam and Puerto Rico have all enacted some types of data breach notification statutes. While this is a positive thing, unfortunately these laws place most of the burden for cybersecurity and protecting employee's and customer's personal information on business owners and employers.
A somewhat recent example is the case of California v. Kaiser Foundation Health Plan, Inc. The suit alleged that Kaiser's “unreasonable delay” in advising affected individuals of an information breach had violated state breach notification law.
Kaiser learned that a computer with a hard drive containing personal information of Kaiser employees had been sold at a thrift store. Kaiser did not admit liability, but agreed to pay $150,000 in penalties and costs. In addition, the Foundation agreed to non-monetary terms such as employee training, review and updating of encryption and related policies, and conducting related periodic audits with reports to the AG’s office.
Security Breaches put Employers at Risk
Businesses and employers are being sued by employees more frequently because of personal information that has been compromised as the result of a security breach. While most companies do take steps to keep personal information secure, having a truly secure system in place along with strict access policies, etc. should be seen as a mandatory function.
Comprehensive measures should be taken to enhance your company's security practices and to comply with all state and federal laws. This will not only protect your employees, but protect your company from possible litigation. Companies employing workers in multiple states must become familiar with the state laws where they operate as these laws do vary widely from state to state.
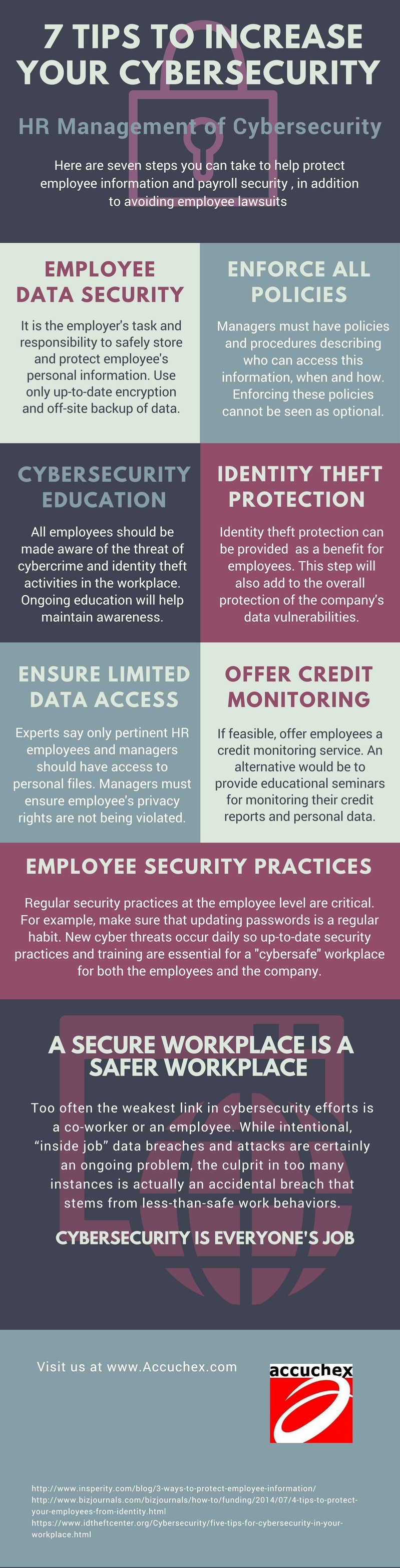
Share this Image On Your Site
Epayroll as a Security Payroll Process Option
As a business owner or payroll manager you have a number of options for your payroll process. You can install software in-house, or use a cloud-based program, both of which offer a good alternative. On the other hand, Paperless Payroll Management Solutions by Accuchex, also known as “Green Payroll” or Epayroll, combines tax payment and direct deposit. With direct deposit and online access and there is no need to have a payroll package delivered every check date.
Outsourcing payroll can save staff time, money and be the best payroll solution for your business. In addition, many payroll services offer related services like insurance solutions, retirement planning, and HR functions.
You can be assured that the accountability and liability for payroll compliance rests with your vendor, freeing you from the constant pressure of staying fully informed and compliant with the ever changing - and growing - rules, regulations, and legislation.
In addition, all wages and tax payments are sent electronically and online access lets you view, print and save all payroll data. Employees have access to their wage history by logging into their own portal; access to complete wage history ensures they will always be able to view their information at their convenience.
Reliability, full-service options, and reputation are the hallmarks of a quality payroll management service provider. If you are currently looking to invest in outsourcing you get your Free Download: Payroll Outsourcing Guide to help you make an informed decision or call Accuchex Payroll Management Services at 877-422-2824.




